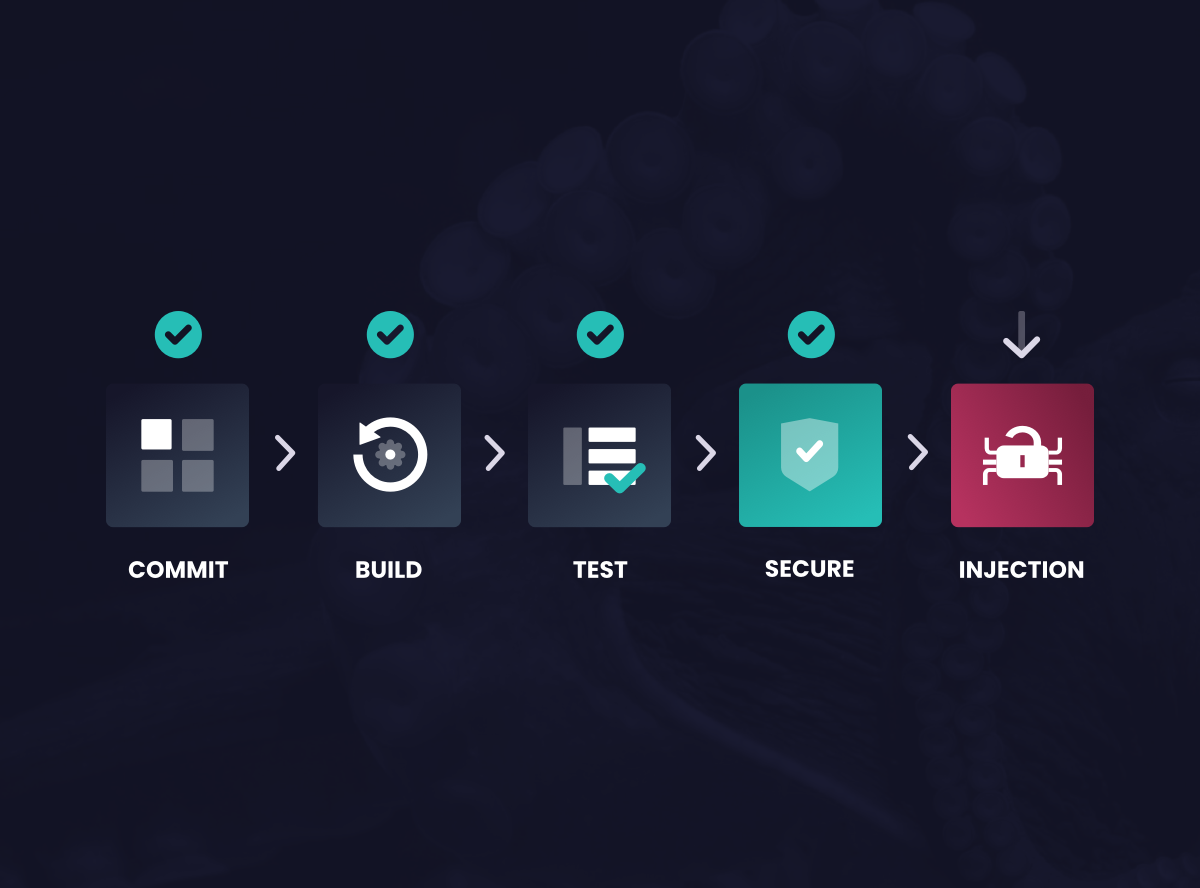
The solution
Security-as-Code is predicated on immutably and continuously securing applications with control through policy. With Waratek’s model around Security-as-Code, organizations can achieve a 100% reduction in false positives, with 100% accuracy at less than a 2% performance impact, changing the economics of application security.
This approach drastically reduces reliance on human intervention and grants security teams autonomy while allowing engineers to focus on development rather than vulnerability remediation.